
Peter has declined to include your fishing shop in his search engine. Delete the search_results table to take revenge (and claim the flag).
Pablo's admin login page was discovered during enumeration. Log in to the admin account to retrieve the flag.
An image archiving web service is vulnerable to XSS.

Pablo has made a logic error while setting up the password handler, exploit this to login to the admin account

A competition giving away a free wheel of cheese is vulnerable to SQL Injection, exploit this to change everyone's email to your address to win the cheese.

A group of hackers have unionized to distrobute pirated indie game titles, extract the admin credentials to teach them a lession.

Pablo the web developer has forgotten to implement input validation on the username parameter.

Pablo has put a list based filter to remove open html tags on the username parameter.
Pablo has stolen your pet fish, pwn to get revenge.
A vibe coded online image viewer is vulnerable to reflected Cross Site Scripting, prove it.
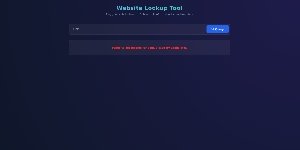
A website preformance checker has made a mistake implementing a regex check.

A cybersecurity forum is ironically vulnerable to stored XSS.

A forum profile page is vulnerable to xss, change it to trigger an alert.
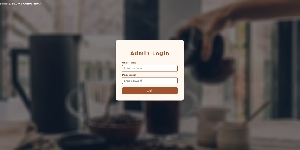
Pablo's admin login page was discovered during enumeration. Log in to the admin account to retrieve the flag.

Peter has declined to include your fishing shop in his search engine. Delete the search_results table to take revenge (and claim the flag).

Pablo has made a logic error while setting up the password handler, exploit this to login to the admin account

A competition giving away a free wheel of cheese is vulnerable to SQL Injection, exploit this to change everyone's email to your address to win the cheese.

A group of hackers have unionized to distrobute pirated indie game titles, extract the admin credentials to teach them a lession.

Pablo the web developer has forgotten to implement input validation on the username parameter.

Pablo has put a list based filter to remove open html tags on the username parameter.
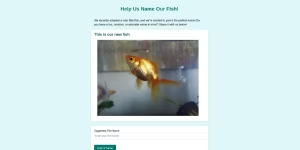
Pablo has stolen your pet fish, pwn to get revenge.
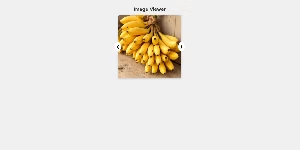
A vibe coded online image viewer is vulnerable to reflected Cross Site Scripting, prove it.
A website preformance checker has made a mistake implementing a regex check.

A cybersecurity forum is ironically vulnerable to stored XSS.

A forum profile page is vulnerable to xss, change it to trigger an alert.
An image archiving web service is vulnerable to XSS.
Raidray CTF offers free and educational hacking sandboxes based on real-world vulnerabilities, bug bounties, exposures, and technologies. Explore a myriad of games based on various techniques such as Cross-Site Scripting (XSS), IDORs, Broken Access Control, and SQL Injection.
In the world of information security, Capture The Flag (CTF) games are a competitive exercise designed to test and sharpen technical skills in a gamified environment. The goal is to find a flag, a specific string of text hidden within the game.
These competitions are the gold standard for hands-on learning, allowing aspiring ethical hackers and seasoned pros to practice offensive and defensive techniques without breaking the law.
Simply click on any of the games above to be placed into a safe environment to test your offensive security skills and tools. A flag is hidden within each game; retrieve the flag and submit it via the Flag Submission page to win.
We often host special events where you can compete against other hackers to win prizes, more information can be found on our community discord.
While we encourage beginners to write their own tools and scripts during training, you are welcome to use whatever you wish. Please do not perform actions that may impact server performance for other users.
We have established this platform to provide students, aspiring cybersecurity professionals, and beginner cybersecurity researchers with an environment to practice offensive security, ethical hacking, penetration testing, and cybersecurity skills in a safe and controlled setting.
Our platform places you in a sandbox with real-world Common Vulnerabilities and Exposures (CVEs), common weaknesses, and real-world data breach scenarios.